Blogs
Navigating the Network: A Comprehensive Guide to Kubernetes Networking Models
Introduction
In the world of Kubernetes, networking is a fundamental aspect that orchestrates communication between various components within and outside the cluster. Understanding Kubernetes networking models is crucial for anyone working with this orchestration tool.
This detailed blog post explores the intricacies of Kubernetes networking, offering insights into how it ensures efficient and secure communication in containerized environments.
Understanding Kubernetes Networking
Kubernetes networking is designed to meet four key requirements, each of which plays a vital role in the functionality and operation of a Kubernetes cluster.
Container-to-Container Communication: This is the fundamental layer of Kubernetes networking. It enables direct communication between containers within the same pod. These containers share the same network namespace, meaning they can communicate with each other using localhost. This setup is crucial for applications that involve multi-container pods, where containers need to interact closely and efficiently.
Pod-to-Pod Communication: In Kubernetes, each pod is allocated a unique IP address. This design choice simplifies the process of enabling communication between pods, regardless of which node they reside on. Pods can communicate with each other without the need for network address translation (NAT), ensuring direct and straightforward connectivity. This model is foundational for creating a distributed system where each pod can function as an independent microservice.
Pod-to-Service Communication: Kubernetes services are a critical abstraction that provides a consistent and reliable way for pods to access other pods. A service is essentially a stable address for a set of changing pods. It ensures that any request directed to the service is automatically and intelligently routed to the right pod, even as pods are created, destroyed, or updated. This layer of abstraction is vital for maintaining a resilient and scalable system.
External-to-Internal Communication: This aspect of Kubernetes networking involves managing inbound traffic from outside the cluster to services within the cluster. It's handled through mechanisms like Ingress controllers and LoadBalancers. These tools allow external users and applications to access services running inside the cluster securely and efficiently. They play a crucial role in exposing applications to end-users and other external systems.
Services and Load Balancing
Services in Kubernetes are essential for providing stable addresses to a group of pods, which may dynamically change over time. They play a critical role in managing access to applications running on pods. Let's delve deeper into the different types of services and their role in load balancing:
ClusterIP: This is the default Kubernetes service. ClusterIP services assign a unique internal IP address which is used to communicate with the service. These are only reachable within the cluster, making them useful for internal communications between pods in the cluster. It's ideal for scenarios where you don't need external access to your services.
NodePort: NodePort services extend ClusterIP's capabilities. In addition to an internal IP, NodePort services make a specific port available on all cluster nodes. External traffic can access the service on these exposed ports, where the traffic is then routed to the appropriate internal IP. This is particularly useful when you need external traffic to access a specific port across all nodes.
LoadBalancer: Building on NodePort, LoadBalancer services integrate with cloud providers' load balancers. This type automatically creates an external load balancer, directing external traffic to the NodePort across your cluster nodes, and then to the correct pods. It simplifies the process of exposing services to the internet and is particularly effective for distributing incoming network traffic, thereby improving the scalability and reliability of applications.
ExternalName: Unlike other types, ExternalName services don't route traffic to pods. Instead, they act as an alias by returning a CNAME record to an external service. This is useful when you want to integrate services within a Kubernetes cluster with external services using DNS.
Network Policies for Security
Network policies in Kubernetes provide an essential layer of security, governing how pods communicate with each other and with other network endpoints. They act as a firewall for pods, allowing users to specify ingress and egress rules based on label selectors and CIDR blocks.
For example, consider a scenario where you have a frontend and a backend service. The backend service should not be accessible from outside the cluster but should allow traffic from the frontend service. You can implement this using a network policy that looks something like this:
yaml
apiVersion: networking.k8s.io/v1
kind: NetworkPolicy
metadata:
name: backend-network-policy
namespace: default
spec:
podSelector:
matchLabels:
app: backend
policyTypes:
- Ingress
ingress:
- from:
- podSelector:
matchLabels:
app: kubeops-frontend
ports:
- protocol: TCP
port: 80
This policy ensures that only pods with the label app: kubeops-frontend can access the backend pods on TCP port 80. Such fine-grained control helps maintain a secure and controlled network environment within Kubernetes.
It's also crucial to consider default behaviors. By default, all pods in a Kubernetes cluster can communicate with each other. Applying a network policy can change this default behavior. For instance, applying a policy that allows specific traffic implies that all other traffic not matching the policy will be denied.
Ingress and Egress Controllers
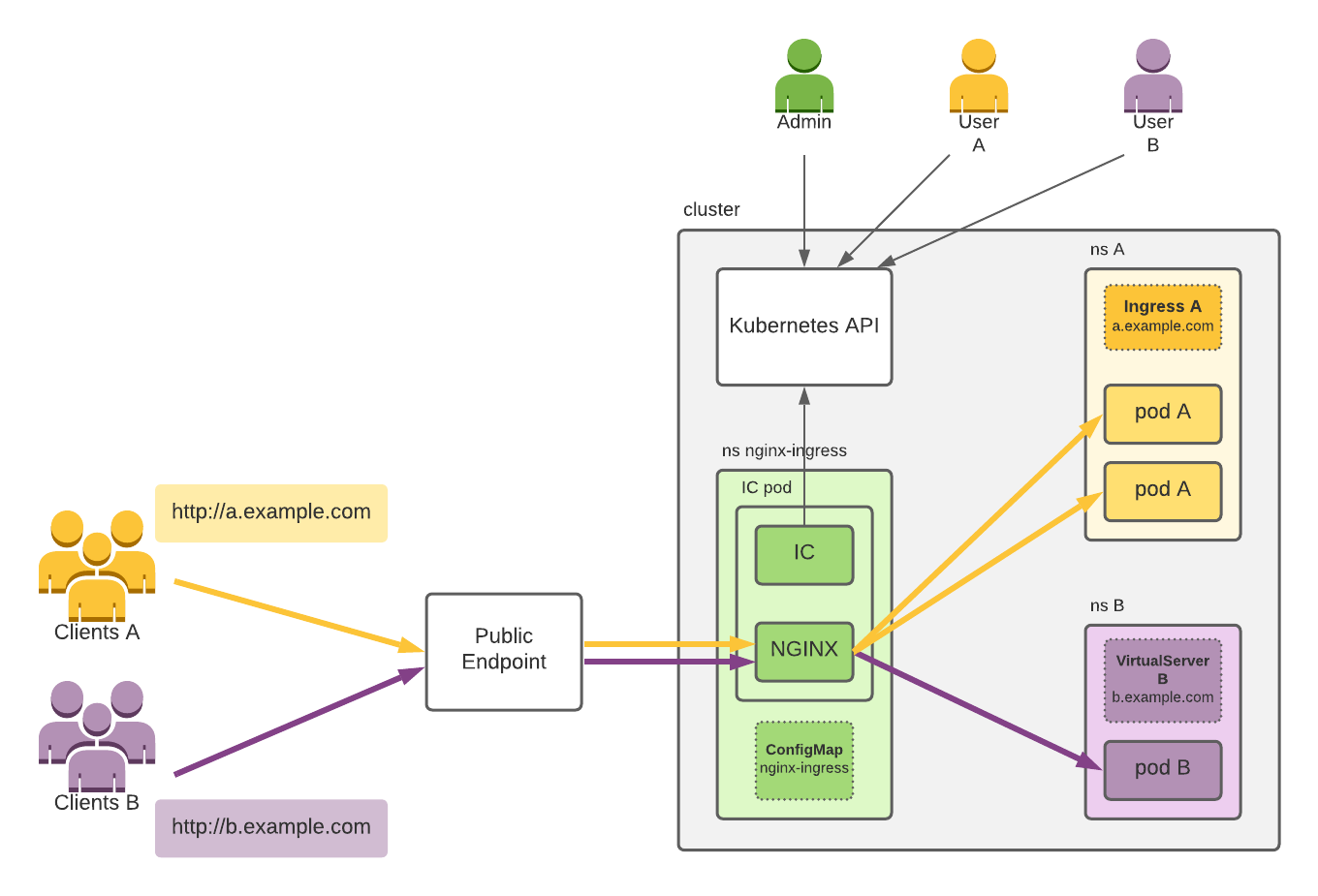
Source: https://docs.nginx.com/nginx-ingress-controller/img/ic-high-level.png
Ingress and Egress Controllers in Kubernetes manage external access to the services within a cluster, typically HTTP. Ingress Controllers facilitate the routing of external traffic to the correct internal resources, while Egress Controllers manage outbound traffic from the cluster.
An Ingress Controller is responsible for reading Ingress Resource information and processing it appropriately. For example, when a user requests a URL, the Ingress Controller routes the request to the appropriate service based on the routing rules defined in the Ingress Resource. This is particularly useful for managing access to microservices and implementing SSL/TLS termination.
Egress Controllers, on the other hand, handle outbound traffic. They ensure that the requests from within the cluster to the outside world are managed and routed correctly. Egress Controllers can enforce policies that limit the destinations to which pods can establish connections, enhancing the cluster's overall security.
Implementing these controllers requires a clear understanding of the network architecture and the traffic patterns of applications. For instance, a well-configured Ingress Controller can efficiently manage traffic spikes, route based on URL paths, and offer name-based virtual hosting.
Core Networking Solutions: Importance and Roles
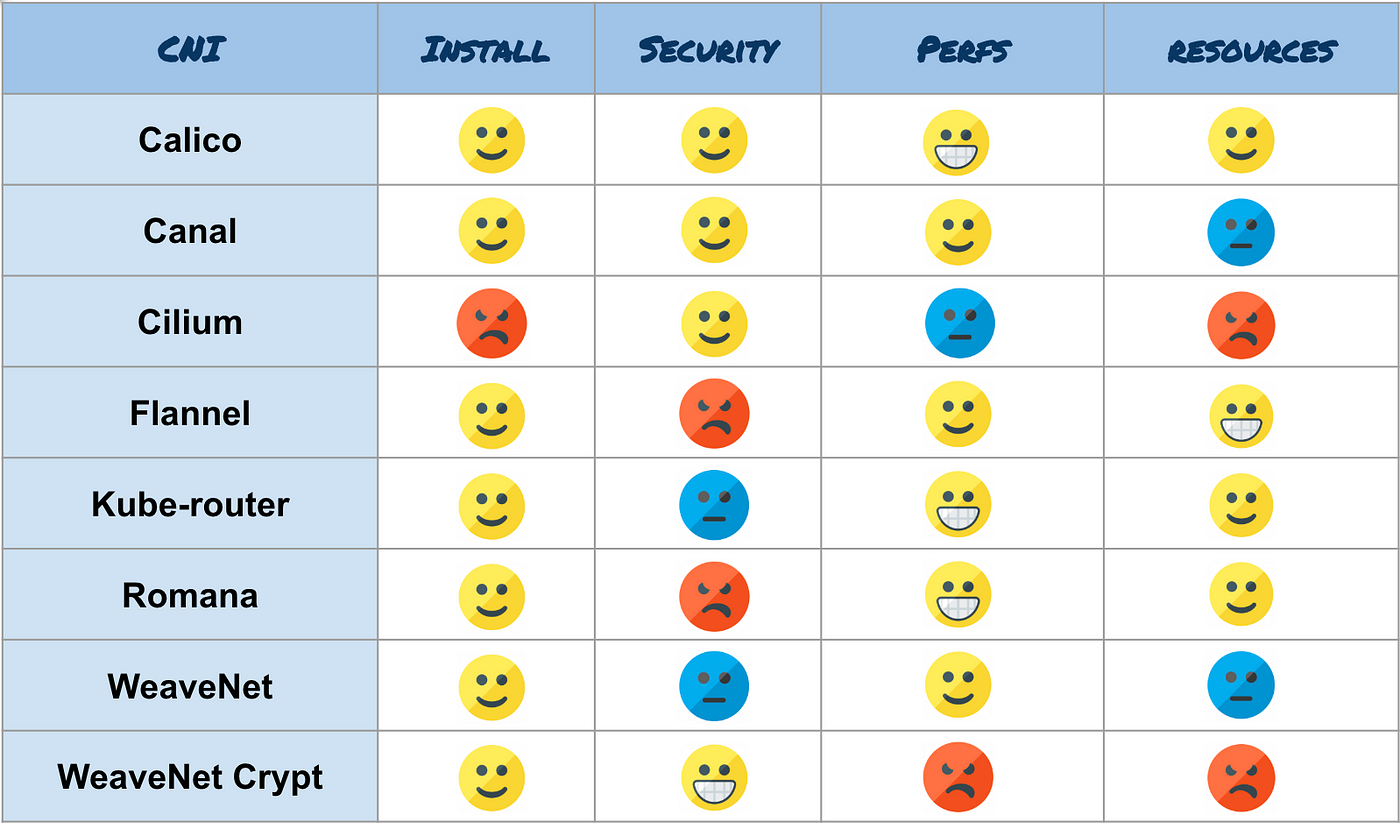
Calico for Network Policy Enforcement: Recognized for its robust network policy enforcement, Calico plays a crucial role in maintaining application security. It provides fine-grained control over pod communication, allowing only authorized traffic, thereby enforcing security policies and segmenting network traffic to prevent unauthorized access. Its significance lies in its ability to enhance the overall security and integrity of network interactions within an application.
Flannel for Simple Overlay Networks: Flannel is vital for its simplicity and efficiency in setting up overlay networks, connecting pods across nodes. Its role is to simplify network configuration in Kubernetes deployments by managing subnet assignments automatically. This reduces the complexity and operational overhead associated with network management, making it a valuable tool for straightforward yet effective network connectivity.
Cilium for API-Aware Networking: Cilium is essential for bringing API-aware network security filtering to Kubernetes. Utilizing BPF, it filters network traffic at the kernel level, understanding Kubernetes labels and metadata. Its role is critical in enhancing security and offering improved visibility into network traffic, especially for microservices, thereby contributing to a more secure and transparent network environment.
Canal as a Combination of Flannel and Calico: Canal merges the best of Flannel and Calico, providing an all-encompassing networking solution for Kubernetes. Its role is to offer both ease of use (from Flannel) and powerful security features (from Calico). This combination makes Canal a versatile choice, catering to the need for both efficient network overlay and flexible network policies.
Kube-router for a Lightweight Solution: Kube-router serves as a simpler, more efficient alternative to standard network solutions. Its role is to handle routing, network policy, and service proxy functions with a single daemon. This makes it an ideal choice for smaller or resource-constrained environments, offering a lightweight yet effective networking solution.
Source: https://miro.medium.com/v2/resize:fit:1400/1*nghpKHLhuUt5c8LYrWpKcQ.png
Best Practices in Kubernetes Networking
- Use Network Policies to Control Traffic Flow: Network policies are essential for securing a Kubernetes environment. They act as a firewall for pods, allowing you to define which pods can communicate with each other. For instance, you might restrict database pods so they can only be accessed by specific application pods, enhancing the security and integrity of your data.
- Implement Service Mesh for Complex Communication: In microservices architecture, a service mesh like Istio or Linkerd provides an additional layer of communication control, observability, and reliability. For example, you can manage load balancing, service-to-service authentication, and monitor inter-service communication through a service mesh, making it easier to debug and optimize your applications.
- Optimize Load Balancing Strategies: Load balancing is crucial for distributing traffic evenly across pods. You can use strategies like round-robin, where requests are distributed sequentially, or a more advanced method like IP hash, which ensures a user's session is consistently served by the same pod. This ensures efficient use of resources and improved user experience.
- Enable DNS for Service Discovery: Kubernetes DNS service plays a critical role in service discovery. It allows pods to locate other pods and services by name, rather than relying on potentially changeable IP addresses. For example, an application can easily locate a database service through its DNS name, simplifying configurations and inter-service communications.
- Leverage Ingress Controllers for External Access: When exposing your services to the external world, Ingress controllers are a more advanced and flexible option than NodePort or LoadBalancer services. They provide HTTP/HTTPS routing, SSL termination, and name-based virtual hosting. This means you can efficiently manage external access to your services with fine-grained control.
- Monitor and Log Network Activity: Continuous monitoring and logging of network traffic are essential for diagnosing issues and ensuring security. Tools like Prometheus for monitoring and Fluentd for logging provide insights into the performance and security of your network. They help you spot anomalies, understand traffic patterns, and make informed decisions about scaling and optimization.
- Adopt IPv6 Networking for Scalability: As the scale of Kubernetes clusters grows, IPv6 networking becomes increasingly relevant. It provides a larger address space, eliminating the need for complex NAT setups. Transitioning to IPv6 can future-proof your cluster by ensuring you have enough IP addresses for all your pods and services.
Conclusion
Kubernetes networking is a pivotal aspect that supports the dynamic and distributed nature of containerized applications. By understanding its models and effectively implementing network policies and services, you can ensure a robust, secure, and efficient environment for your Kubernetes cluster.

